名称空间解释
名字是啥?
答:集群中每个对象的名称对于该类型的资源都是唯一的。并且每一个对象在整个集群中也有一个唯一的UID.
名称空间是啥?
答:名称空间将集群划分为多个领域
什么时候使用?
答: 企业中有多人使用时候,可以进行权限管控
怎么查看?
答:看输出 是false 还是 true
kubectl api-resources --namespace=false
kubectl api-resources --namespace=true
名称空间和dns的关系?
答:
创建服务时,它将创建相应的DNS条目,这个条目的形式是<service-name>.<namespace-name>.svc.cluster.local
上面的namespace-name 是啥就是啥
默认的名称空间?
答:
[root@k8s-01 ~]# kubectl get namespace
NAME STATUS AGE
default Active 2d10h
kube-flannel Active 2d10h
kube-node-lease Active 2d10h
kube-public Active 2d10h
kube-system Active 2d10h
[root@k8s-01 ~]# kubectl get ns
NAME STATUS AGE
default Active 2d10h
kube-flannel Active 2d10h
kube-node-lease Active 2d10h
kube-public Active 2d10h # 保留给集群使用,保持基本使用
kube-system Active 2d10h #管理相关的组件
kubectl get pod -n kube-system
kubectl describe -n kube-system
如何新增一个名称空间
答:如下命令
[root@k8s-01 ~]# kubectl create ns dev
namespace/dev created
[root@k8s-01 ~]# kubectl get ns
NAME STATUS AGE
default Active 2d10h
dev Active 6s
kube-flannel Active 2d10h
kube-node-lease Active 2d10h
kube-public Active 2d10h
kube-system Active 2d10h
[root@k8s-01 ~]# kubectl delete ns dev
如何利用json 创建名称空间
答:
[root@k8s-01 chapter06]# kubectl apply -f namespace-dev.json
namespace/development created
[root@k8s-01 chapter06]# kubectl app^C
[root@k8s-01 chapter06]# kubectl apply -f namespace-prod.json
namespace/production created
[root@k8s-01 chapter06]# kubectl get ns
NAME STATUS AGE
default Active 2d10h
development Active 17s
kube-flannel Active 2d10h
kube-node-lease Active 2d10h
kube-public Active 2d10h
kube-system Active 2d10h
production Active 4s
[root@k8s-01 chapter06]# kubectl get ns --show-labels
NAME STATUS AGE LABELS
default Active 2d10h <none>
development Active 35s name=development
kube-flannel Active 2d10h k8s-app=flannel,pod-security.kubernetes.io/enforce=privileged
kube-node-lease Active 2d10h <none>
kube-public Active 2d10h <none>
kube-system Active 2d10h <none>
production Active 22s name=production
[root@k8s-01 chapter06]# cat namespace-prod.json
{
"apiVersion": "v1",
"kind": "Namespace",
"metadata": {
"name": "production",
"labels": {
"name": "production"
}
}
}[root@k8s-01 chapter06]# cat namespace-dev.json
{
"apiVersion": "v1",
"kind": "Namespace",
"metadata": {
"name": "development",
"labels": {
"name": "development"
}
}
}
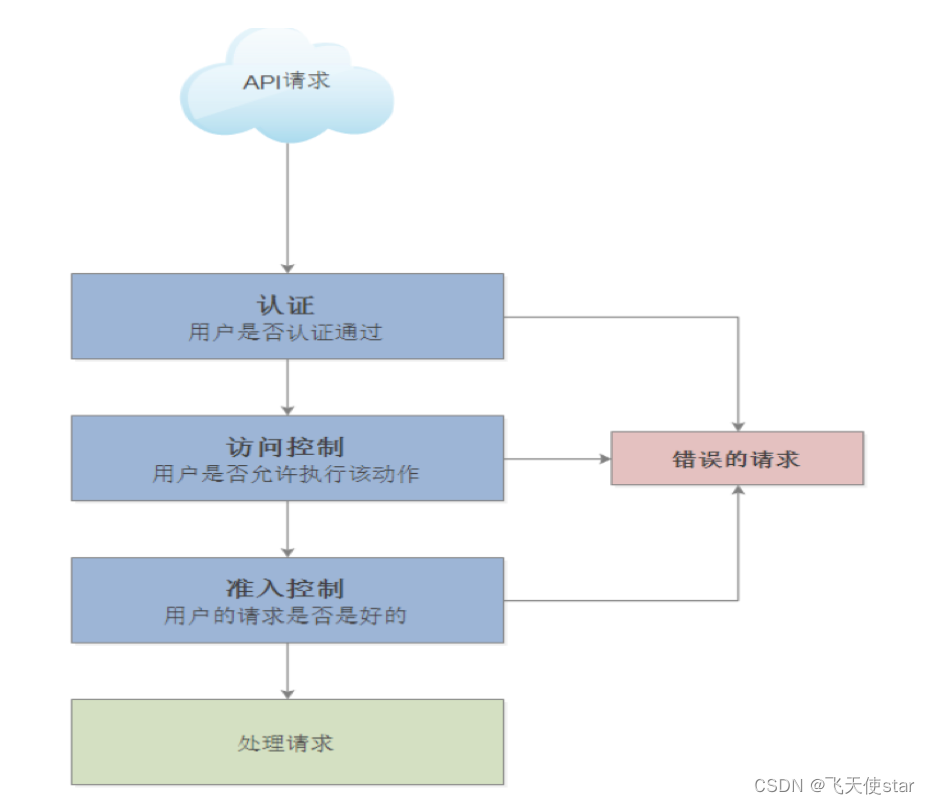
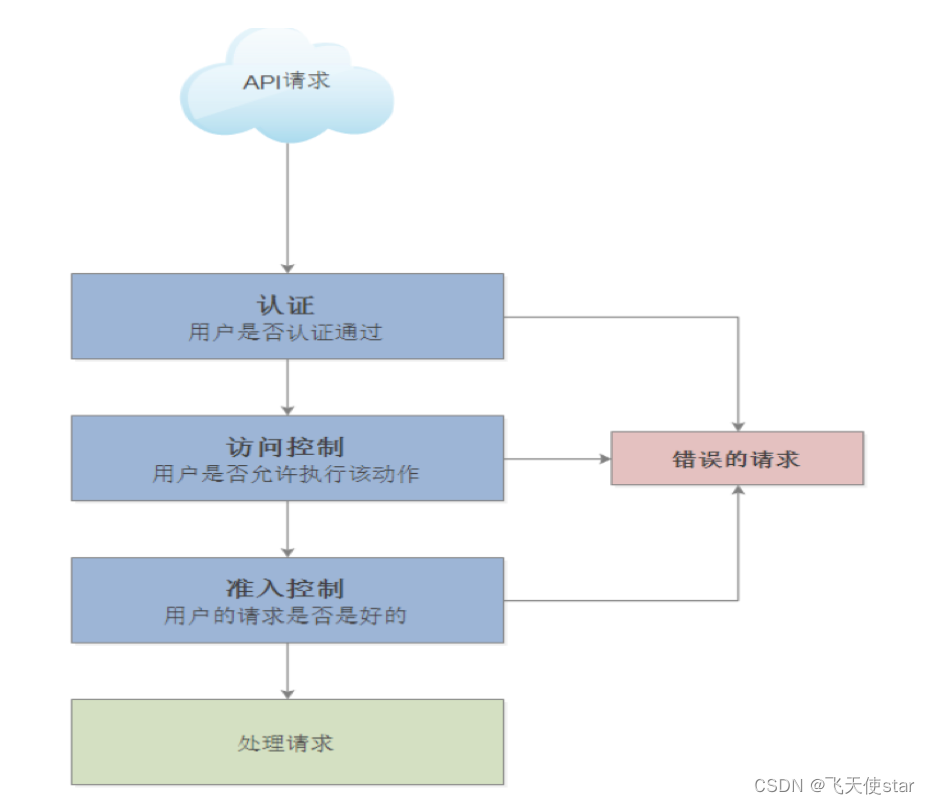
访问kubernetes API的控制
2. 认证的三种类型
基本认证
基于证书的验证
基于OpenID Connect
3. 授权请求
如果Bob有以下策略,那么它可以读取projectCaribou名称空间的Pods
{
"apiVersion": "abac.authorization.kuberneres.io/vibeta1",
"kind": "Policy",
"spec": {
"user": "bob",
"namespace": "projectCaribou",
"resource": "pods",
"readonly": true
}
}
如果Bob发出以下请求,则请求将被授权,因为它可以读取projecctCaribou名称空间的对象。
准入控制(有这块功能,使用场景少)
允许控制模块是可以修改或拒绝请求的软件模块。除了授权模块可用的属性之外 ,允许控制模块还可以访问正在创建或更新的对象的内容。
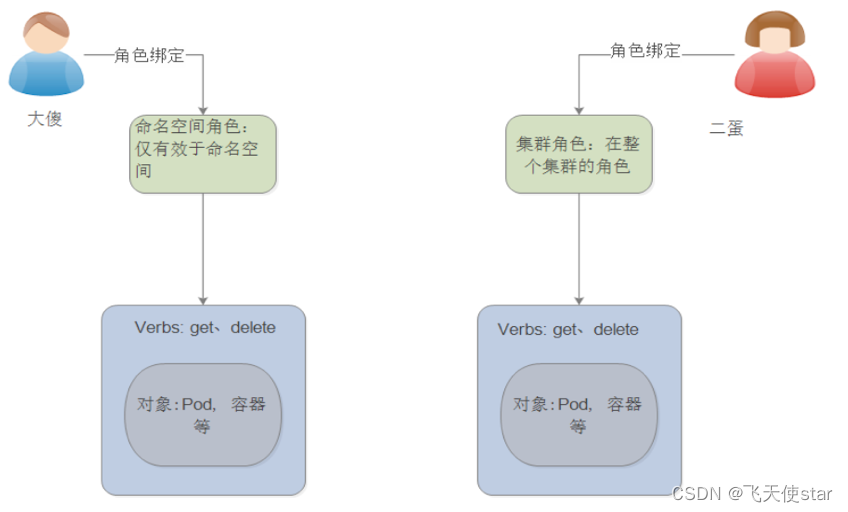
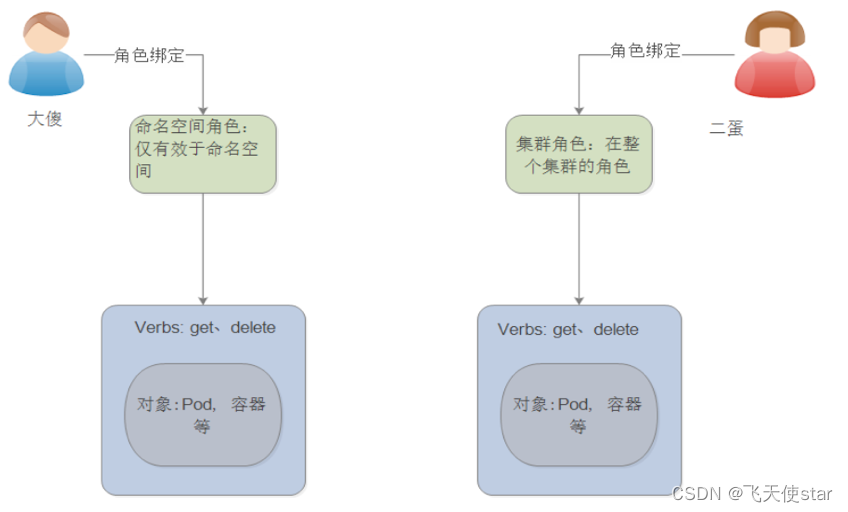
RBAC的介绍
为了充分理解RBAC的思想,我们必须理解它包含的三个要素:
Subject
Resources
Verbs
人,资源,对资源有啥控制权限方向理解
verbs 有普通的角色和集群的角色
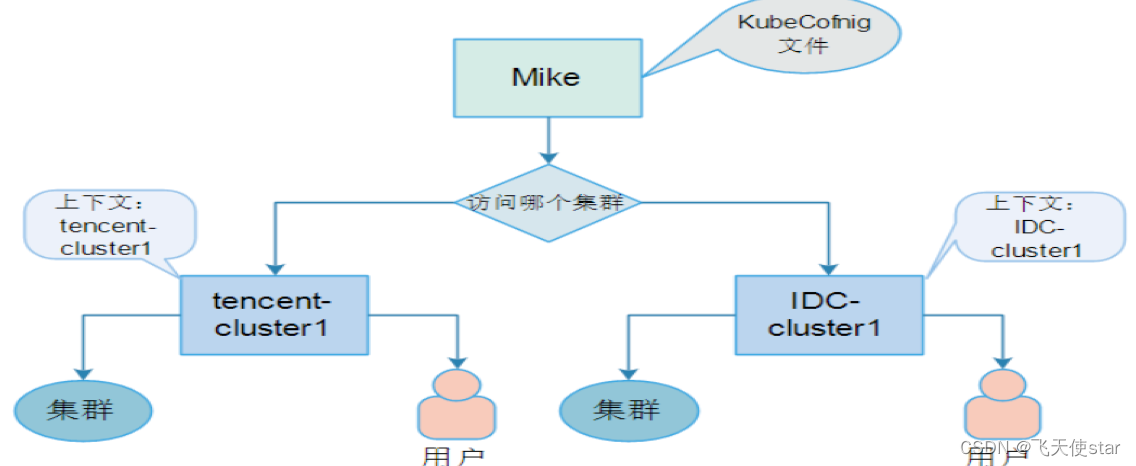
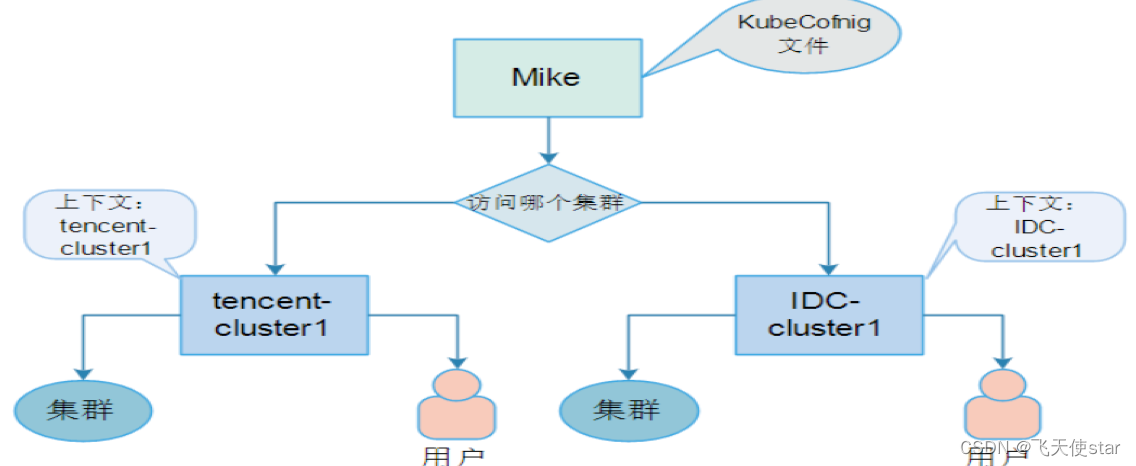
kubeconfig
Kubeconfig文件记录如何进行身份验证的详细信息。Kubectl使用这个配置文件来确定api服务器在何处及如何向api服务器发出请求。
Kubeconfig文件三个顶级结构:
用户
Cluster属性
Context
查看授权文件: cat ~/.kube/config
有没有演示案例?
答:
[root@k8s-01 chapter06]# kubectl config set-credentials cluster-admin --username=admin --password=123456
User "cluster-admin" set.
[root@k8s-01 chapter06]# kubectl config set-credentials regular-user --username=user --password=654321
User "regular-user" set.
[root@k8s-01 chapter06]# kubectl config set-cluster cluster1 --server=https://192.168.1.1
Cluster "cluster1" set.
[root@k8s-01 chapter06]# kubectl config set-cluster cluster2 --server=https://192.168.1.2
Cluster "cluster2" set.
用户名和集群配置完毕
上下文将用户名和密码关联起来
[root@k8s-01 chapter06]# kubectl config set-context cluster-regular --cluster=cluster2 --user=regular-user
Context "cluster-regular" created.
[root@k8s-01 chapter06]# kubectl config set-context cluster-admin --cluster=cluster1 --user=cluster-admin
Context "cluster-admin" modified.
查看配置
root@k8s-01 chapter06]# kubectl config view
apiVersion: v1
clusters:
- cluster:
server: https://192.168.1.1
name: cluster1
- cluster:
server: https://192.168.1.2
name: cluster2
- cluster:
certificate-authority-data: DATA+OMITTED
server: https://192.168.100.30:6443
name: kubernetes
contexts:
- context:
cluster: cluster1
user: cluster-admin
name: cluster-admin
- context:
cluster: cluster2
user: regular-user
name: cluster-regular
- context:
cluster: kubernetes
user: kubernetes-admin
name: kubernetes-admin@kubernetes
current-context: kubernetes-admin@kubernetes
kind: Config
preferences: {}
users:
- name: cluster-admin
user:
password: "123456"
username: admin
- name: kubernetes-admin
user:
client-certificate-data: REDACTED
client-key-data: REDACTED
- name: regular-user
user:
password: "654321"
username: user
切换上下文
[root@k8s-01 chapter06]# kubectl config use-context cluster-admin
Switched to context "cluster-admin".
[root@k8s-01 chapter06]# kubectl get pod
^C
切换到其他的上下文是没有内容的
[root@k8s-01 chapter06]# kubectl config use-context kubernetes-admin@kubernetes
Switched to context "kubernetes-admin@kubernetes".
如何删除用户?
kubectl config unset user.regular-user
kubectl config delete-context cluster-admin
用户的创建
此处实验做错了,可以参考,如果后续在大公司,人员多的情况下,在来复盘,小公司一般不需要
yum install -y openssl
openssl genrsa -out mike.key 2048
openssl req -new -key mike.key -out mike.csr -subj "/CN=mike/O=devs"
[root@k8s-01 keys]# openssl x509 -req -in mike.csr -CA /etc/kubernetes/pki/ca.crt -CAkey /etc/kubernetes/pki/ca.key -CAcreateserial -out mike.crt -days 365
Signature ok
subject=/CN=mike/O=devs
Getting CA Private Key
查看集群配置信息 kubectl config view
[root@k8s-01 keys]# kubectl config set-cluster mike --certificate-authority=ca.crt --server=https://192.168.100.30:6443
Cluster "mike" set.
[root@k8s-01 keys]# kubectl config set-credentials mike --client-certificate=mike.crt --client-key=mike.key
User "mike" set.
[root@k8s-01 keys]# kubectl config set-context mike --cluster mike --user mike
集群默认角色
[root@k8s-01 keys]# kubectl describe clusterrole cluster-admin
Name: cluster-admin
Labels: kubernetes.io/bootstrapping=rbac-defaults
Annotations: rbac.authorization.kubernetes.io/autoupdate: true
PolicyRule:
Resources Non-Resource URLs Resource Names Verbs
--------- ----------------- -------------- -----
*.* [] [] [*]
[*] [] [*]
验证Mike的权限
# kubectl config use-context kubernetes-admin@kubernetes
# kubectl get all
其它的验证方法
# kubectl auth can-I get pods –-as mike
查看角色
# kubectl get roles
查看Clusterroles
# kubectl get clusterroles
View集群角色
# kubectl describe clusterrole view
Edit集群角色
# kubectl describe clusterrole edit
Admin集群角色
# kubectl describe clusterrole admin
cluster-admin
# kubectl describe clusterrole cluster-admin
创建角色绑定
# kubectl create rolebinding mike --clusterrole view –-user mike --namespace default --save-config
# kubectl get rolebindings
验证mike权限
# kubectl describe rolebinding mike
# kubectl --namespace kube-system describe rolebinding mike
# kubectl auth can-I get pods –-as mike
# kubectl auth can-I get pods --as mike --all-namespaces
删除角色绑定
# kubectl delete rolebinding mike
创建集群所有命名空间查看权限
创建集群角色绑定
# kubectl create –f crb-view.yml --record --save-config
# kubectl describe clusterrolebinding view
验证集群角色绑定
# kubectl auth can-I get pods –-as mike --all-namespaces
创建指定命名空间管理权限
创建角色绑定
# kubectl create –f rb-dev.yml --record --save-config
验证权限
# kubectl --namespace dev auth can-I create deployments --as mike
# kubectl –-namespace dev auth can-I delete deployments --as mike
# kubectl --namespace dev auth can-I “*”“*” --as mike
创建指定名称空间超级管理权限
创建角色绑定
# kubectl create –f rb-mike.yml --record --save-config
测试权限
# kubectl –-namespace mike auth can-I ”*” “*” --as mike
创建自定义权限
- 创建角色和绑定
# kubectl create –f crb-release-manager.yml --record --save-cconfig
# kubectl describe clusterrole release-manager
测试权限
# kubectl –-namespace default auth can-I “*” pods –-as mike
# kubectl –-namespace default auth can-I create deployments –-as mike
# kubectl –-namespace default auth can-I delete deployments –-as mike
给组创建授权
创建一个用户,所属组devs
# openssl req –in keys/mike.csr –noout –subject subject=/CN=mike/O=devs
创建组绑定
# kubectl apply –f groups.yml –-record
# kubectl –-namespace dev auth can-I create deployments –-as mike
客户端执行
# kubectl config use-context mike
# kubectl –-namespace dev run new-db –-image mongo:3.3
针对pod配置服务账户
查看默认的服务帐户
# kubectl get pods/<podname> - yaml
# kubectl get serviceaccounts
创建服务帐户
# kubectl apply –f <<EOF
apiVersion: v1
Kind: ServiceAccount
Metadata:
name: build-robot
EOF
查看创建的服务帐户
# kubectl get serviceaccounts/build-robot –o yaml
删除服务帐户
# kubectl delete serviceaccount/build-robot
参考文档
https://edu.csdn.net/course/detail/27762